Access Matrix and Capability Lists in Computer Security
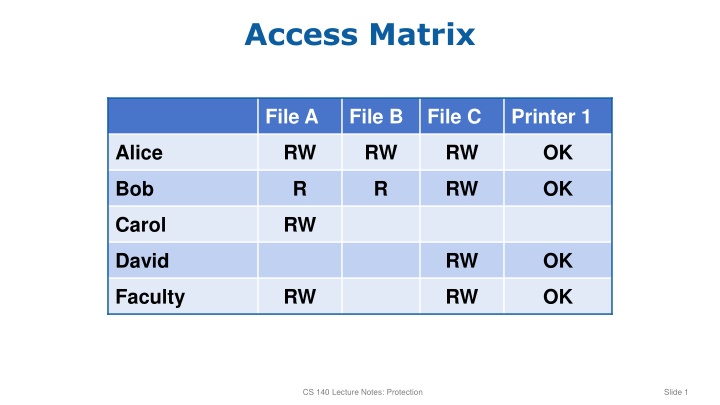
Explore access control mechanisms such as access matrices, capability lists, and their implications for sharing and communication in computer security. Dive into the intricate details of permissions assigned to users like Alice, Bob, Carol, David, and Faculty.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
Access Matrix File A File B File C Printer 1 Alice RW RW RW OK Bob R R RW OK Carol RW David RW OK Faculty RW RW OK CS 140 Lecture Notes: Protection Slide 1
Access Matrix File A File B File C Printer 1 Alice RW RW RW OK Bob R R RW OK Carol RW David RW OK Faculty RW RW OK Access Control List CS 140 Lecture Notes: Protection Slide 2
Access Matrix File A File B File C Printer 1 Alice RW RW RW OK Bob R R RW OK Carol RW David RW OK Faculty RW RW OK Capability List CS 140 Lecture Notes: Protection Slide 3
Capability Lists Alice s capabilities Bob s capabilities Sharing and communication impossible! CS 140 Lecture Notes: Protection Slide 4
Capability Lists Alice s capabilities Bob s capabilities Shared object Shared capability list CS 140 Lecture Notes: Protection Slide 5