February 2022 SIG Update on Log4j Vulnerability Mitigation
Stay informed about the Log4j 2.x vulnerability affecting all versions of SBM and the steps to mitigate the risk by updating to the latest version. Learn about reload4j as an alternative solution and get details on the vulnerability fixes.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
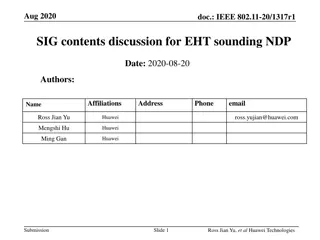
February 2022 SIG Update on log4j Dave Easter Director of Product Management Pete Dohner - SBM R&D Senior Manager Tuesday, February 15, 2022
Housekeeping During the presentations, please type questions into the questions panel We hope to un-mute your microphones during the open Q&A The SIG will be recorded It will be posted on the SIG forum https://community.microfocus.com/it_ops_mgt/sbm/f/sbm_user_group The next SIG will be in March enter your ideas/requests for topics into the questions panel 2
Log4j TL;DR 2.x vulnerability All versions of SBM are affected The vulnerability can be mitigated in the field by installing the latest 2.x log4j 1.x vulnerability SBM is not affected by the 1.x vulnerability Concerned customers can still take action by replacing log4j with reload4j 3
Details on the log4j 2.x vulnerability Fixed in 2.15.0 CVE-2021-44228: Apache Log4j2 JNDI features do not protect against attacker controlled LDAP and other JNDI related endpoints. 2.16.0 CVE-2021-45046: Apache Log4j2 Thread Context Lookup Pattern vulnerable to remote code execution in certain non-default configurations 2.17.0 CVE-2021-45105: Apache Log4j2 does not always protect from infinite recursion in lookup evaluation 2.17.1 CVE-2021-44832: Apache Log4j2 vulnerable to RCE via JDBC Appender when attacker controls configuration. Initial fix was to modify the COMMON_CONFIG.BAT on every system running SBM Tomcat. Customers were concerned it could be set back by a bad actor If you took this step, it is not necessary to back this out. Secondary fix was to remove the JndiLookup class from the log4j- core-*.jar file per CVE-2021-45046. As you replace the log4j with version 2.17.1, this will undo what we did before. 4
Log4j 2.x current mitigation We ve now tested and confirmed that SBM can be manually updated to log4j 2.17.1 Stop Tomcat services Downloaded the latest log4j2 jars (at the moment 2.17.1) Open File Explorer and go to this directory: [SBM Install Dir]\Common\tomcat\lib Remove old version log4j-core-2.XX.X.jar, log4j-api-2.XX.X.jar, log4j-jul-2.XX.X.jar Copy the new files into this directory: log4j-core-2.17.1.jar, log4j-api-2.17.1.jar, log4j-jul-2.17.1.jar Update bat files (run_in_console.bat, update_tomcat_config.bat) with new version number. Run update_tomcat_config.bat (run in admin mode) Start Tomcat 1. 2. 3. 4. 5. 6. 7. 8. 5
1.X vulnerability What is reload4j? https://reload4j.qos.ch/ (ch domain is Switzerland) Initiated by Ceki G lc , the original author of Apache log4j 1.x A fully and currently supported fork of log4j A drop-in replacement of log4j.jar with reload4j.jar in a build requires no source code changes in .java files Should remove scanner findings Reload4j is not a means to obscure security issues. All known Log4j v1 CVEs have been addressed and validated via source code history and review. 6
Log4j 1.x mitigation Again, SBM is not affected by the 1.x vulnerability Some security officers will still want log4j 1.x removed Primarily concerned about log4j 1.x not being supported by Apache anymore Reload4j should address the concerns In addition, the next version of SBM (Q4 CY22) will upgrade 1.x to 2.x Reload4j replacement steps are documented in the knowledge-base article 7
In summary Apply the 2.x mitigation immediately 1.x mitigation is optional Both are addressed in the Q4 CY22 release If you upgrade prior to the Q4 CY22 release, you ll have to reapply the mitigations 8