Mustansiriyah University Cryptographic Hash Functions Course Overview
Explore the detailed structure and components of the SHA-512 algorithm taught in Mustansiriyah University's Faculty of Engineering, including message preparation, word expansion, compression functions, round structure, buffer register values, and constants used in SHA-512. Lectured by Fatimah Al-Ubaidy, this course delves into data security and computer engineering concepts crucial for third-year students.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author. If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
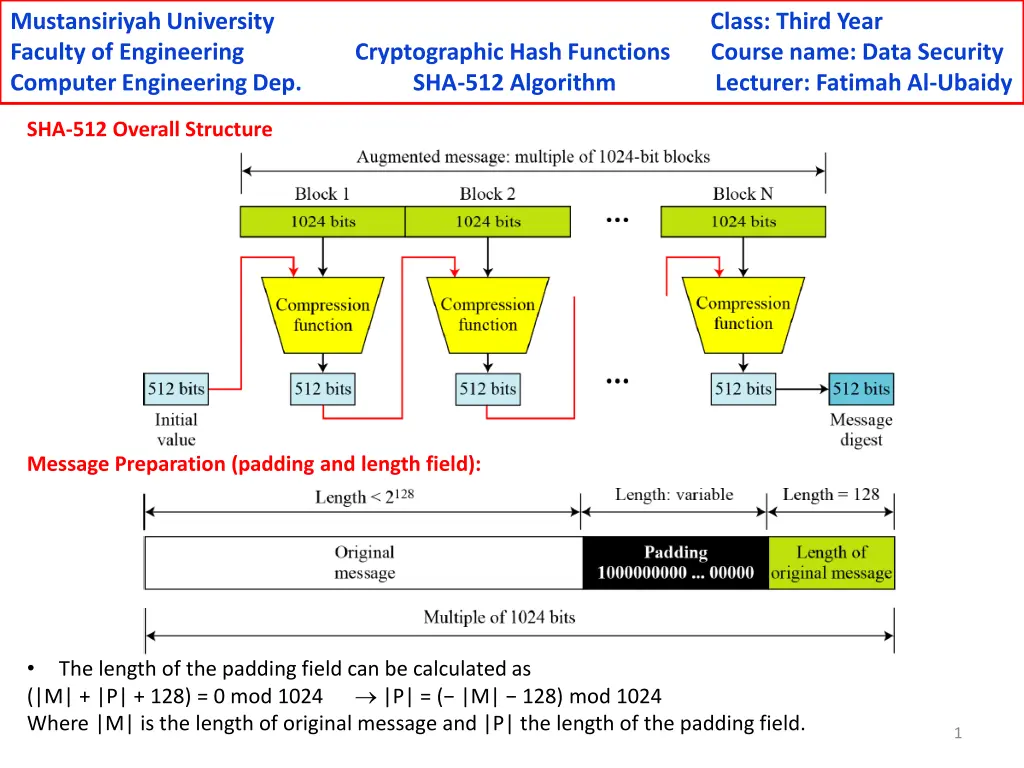
Mustansiriyah University Faculty of Engineering Cryptographic Hash Functions Course name: Data Security Computer Engineering Dep. SHA-512 Algorithm Lecturer: Fatimah Al-Ubaidy Class: Third Year SHA-512 Overall Structure Message Preparation (padding and length field): (|M| + |P| + 128) = 0 mod 1024 Where |M| is the length of original message and |P| the length of the padding field. The length of the padding field can be calculated as |P| = ( |M| 128) mod 1024 1
Mustansiriyah University Faculty of Engineering Cryptographic Hash Functions Course name: Data Security Computer Engineering Dep. SHA-512 Algorithm Lecturer: Fatimah Al-Ubaidy Class: Third Year Processing block and its digest as word Word Expansion: Wi is the processing word of the current round i 2
Mustansiriyah University Faculty of Engineering Cryptographic Hash Functions Course name: Data Security Computer Engineering Dep. SHA-512 Algorithm Lecturer: Fatimah Al-Ubaidy Class: Third Year SHA-512 Compression Function: Kiis a constant variable at round i where i =0,1 79. 3
Mustansiriyah University Faculty of Engineering Cryptographic Hash Functions Course name: Data Security Computer Engineering Dep. SHA-512 Algorithm Lecturer: Fatimah Al-Ubaidy Class: Third Year Structure of each round in SHA-512: A = T1 + T2 B = A C = B D = C E = D + T1 F = E G = F H = G T1 = H + conditional(E,F,G) + rotate(E) + Wi + Ki T2 = majority(A,B,C) + rotate(A) T1 T2 4
Mustansiriyah University Faculty of Engineering Cryptographic Hash Functions Course name: Data Security Computer Engineering Dep. SHA-512 Algorithm Lecturer: Fatimah Al-Ubaidy Class: Third Year The initial values of the buffer registers as 64-bit each a = 6A09E667F3BCC908 e = 510E527FADE682D1 b = BB67AE8584CAA73B f = 9B05688C2B3E6C1F c = 3C6EF372FE94F82B g = 1F83D9ABFB41BD6B d = A54FF53A5F1D36F1 h = 5BE0CD19137E2179 Eighty constants used for the eighty rounds in the SHA-512 5