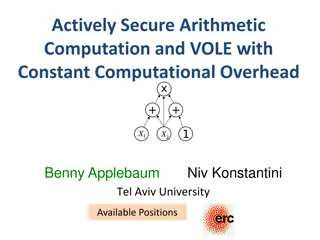
Secure Computation Lecture 6 - Secrets Sharing and Circuit Evaluation
This content discusses secure computation techniques such as secret sharing and circuit evaluation. It covers linear and non-linear aspects of Shamir Secret Sharing, multiplication of shared secrets, and secure circuit evaluation with examples.
Download Presentation

Please find below an Image/Link to download the presentation.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.If you encounter any issues during the download, it is possible that the publisher has removed the file from their server.
You are allowed to download the files provided on this website for personal or commercial use, subject to the condition that they are used lawfully. All files are the property of their respective owners.
The content on the website is provided AS IS for your information and personal use only. It may not be sold, licensed, or shared on other websites without obtaining consent from the author.
E N D
Presentation Transcript
Secure Computation (Lecture 6) Arpita Patra
(n,t) Secret Sharing s : (n,t) Secret Sharing of secret s Linear For MPC: Linear (n,t) Secret Sharing Linearity: The parties can do the following s1 s2 s1 s2 from c: public constant c s s from
Linearity of (n, t) Shamir Secret Sharing each party does locally a a1 + a2 + a3 + b3 b2 b1 b1 b b2 b3 b a3 a2 a1 a c1 c2 c3 1 2 3
Linearity of (n, t) Shamir Secret Sharing c3 c2 a a1 + a2 + a3 + c1 b3 a+b b2 b1 b1 b b2 b3 b a3 a2 a1 a c1 c2 c3 1 2 3 a+b Addition is Absolutely free
Linearity of (n, t) Shamir Secret Sharing a1 a2 a3 d3 a d2 d1 c a a3 a2 c c c a1 a c a 1 2 3 d1 d2 d3 c is a publicly known constant Multiplication by public constants is Absolutely free
Non-linearity of (n, t) Shamir Secret Sharing d2 d3 a b a1 a2 a3 a d1 b3 b2 b1 b1 b2 b3 b b a3 a2 a1 a d1 d2 d3 a b 1 2 3 Come up with example. Multiplication of shared secrets is not free
Secure Circuit Evaluation x1 x2 x3 x4 c y
Secure Circuit Evaluation 2 1 5 9 3 y
Secure Circuit Evaluation 1. (n, t)- secret share each input 1 5 9 2 3
Secure Circuit Evaluation 1. (n, t)- secret share each input 1 5 9 2 2. Find (n, t)-sharing of each intermediate value 3
Secure Circuit Evaluation 1. (n, t)- secret share each input 1 5 9 2 2. Find (n, t)-sharing of each intermediate value 45 3 3 48 144
Secure Circuit Evaluation 1. (n, t)- secret share each input 1 5 9 2 2. Find (n, t)-sharing of each intermediate value Linear gates: Linearity of Shamir Sharing - Non-Interactive 45 3 3 48 144
Secure Circuit Evaluation 1. (n, t)- secret share each input 1 5 9 2 2. Find (n, t)-sharing of each intermediate value Linear gates: Linearity of Shamir Sharing - Non-Interactive 45 3 3 Non-linear gate: Require degree- reduction Technique. Interactive 48 144
Secure Multiplication Gate Evaluation x y x y P1 x1 y1 =z1 y1 x1 Shamir-share z1 P2 y2 x2 Shamir-share x2 y2 =z2 z2 z3 y3 P3 x3 y3 =z3 x3 Shamir-share zn Shamir-share xn yn = zn f1 (x) f2 (x) of degree 2t with x y as its constant term Pn yn xn f1 (x) f2 (x)
Secure Circuit Evaluation Privacy follows (intuitively) because: 1 5 9 2 1. No inputs of the honest parties are leaked. 45 3 3 2. No intermediate value is leaked. 48 144